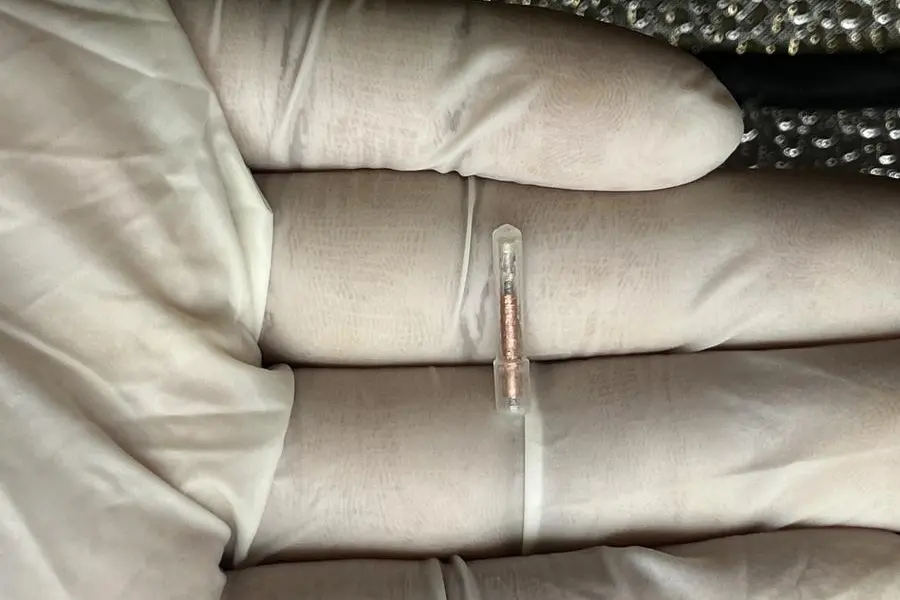
Dubai, UAE – A highly sophisticated malware, known as Operation Triangulation, has recently been unveiled, revealing the covert surveillance capabilities it granted to attackers. This cyberattack specifically targeted iOS devices through iMessage, employing a spyware implant named TriangleDB.
Operation Triangulation operates discreetly, leaving no trace of its activities on the infected devices upon reboot.
The malware gained prominence following an extensive six-month investigation by Kaspersky, a cybersecurity and digital privacy company, which delved into the intricacies of the attackers’ exploitation techniques.
TriangleDB, the implant deployed in Operation Triangulation, exploited a kernel vulnerability to obtain root privileges on the targeted iOS devices. Once successfully deployed, the implant operated solely in the device’s memory, erasing any evidence of its presence upon reboot. This characteristic posed a significant challenge in detecting and removing the implant from the infected devices.
In the absence of a reboot, TriangleDB automatically uninstalled itself after 30 days, unless the attackers extended the timeframe. Acting as a sophisticated spyware, TriangleDB facilitated extensive data collection and monitoring activities.
Within the implant, a total of 24 commands were identified, each serving a distinct purpose. These commands enabled the attackers to interact with the device’s filesystem, manipulate processes, extract victim credentials from the keychain, monitor geolocation, and perform other functions. Also, during the analysis of TriangleDB, signs suggesting the potential for a similar implant targeting macOS devices were discovered.
The spyware reveals the evolving landscape of targeted attacks, underscoring the need for robust cybersecurity measures to safeguard against such threats.